It's mainly divided into two main configurations, one to be done in your domain controller( or any member server) and one to be done in your Cisco router or switch.
1- Windows configuration:
We have to configure RADIUS on a Windows memeber server or domain controller:
go to add/remove windows components:

Now you can configure IAS from the administrative tools in control panel:

right-click RADIUS Clients, and select New RADIUS Client

Name is any friendly name, and IP is the ip address for the interface which connected to the same network where the Radius server exist.
Now we have to create a remote access policy.
name it anyname ! and choose custom:

Click add and choose Windows-groups.
click add again, and choose a windows group (this group will be the only one which have access to your routers!, you can add more groups later, but i don't recommend adding everyone!)

Then click Ok.
Select grant:

Then click next and Edit Profile:

select the Authentication tab.
Check Unencrypted Authentication (PAP/SPAP), and uncheck all the rest.

Then select the advanced tab.
Select Service-Type, then click Edit,
In the Enumerable Attribute Information dialog box
select login from the attribute value

Then click ok,
in advanced tab choose frame protocol and then choose remove.

Now you have to click ok, and when IAS ask you whether you would like to see help or not, its up to you for sure whether you like to see it or not :-).
Now we finished the Windows configuration, and we have to move to the router configuration.
2-Router configuration:
Ill assume that you are familiar with cisco commands and modes, and you know your interfaces!
First of all we have to have secret password enabled.
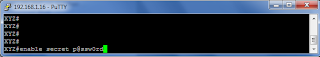
Then we have to configure our router for RADIUS authentication.
aaa anyrouter
radius-server host 192.168.1.16 auth-port 1645 acct-port 1646 key cisco (the key must be the same as the one which we configured in Windows RADIUS installation.)
ip radius source-interface f0/0 (you know your interface which with the RADIUS!)
aaa authentication login mylist group radius local (mylist could be any list even the default)
Let's add a local user now, to use it in case we couldn't access the Radius server!
Now we have to configure lines to use the list which we created earlier (mylist)
#line vty 0 4
#login authentication mylist
We have to set a host name for the router:
#hostname xyz
then we have to configure our domain:
#ip domain-name roseicollis.net
Then,lets generate the crypto keys:
#crypto key generate rsa
Finally lets restrict our lines to use SSH instead of telnet (Remember you have to use Putty to access it remotely)
# Line vty 0 4
# Transport input ssh
Now if everything worked well, you can use any user from the group which enabled in Radius, and its associated password (remember you use just the user name only not followed by@domain name nor domainname\username format)



No comments:
Post a Comment